Technology moves fast. Risk moves faster. That is why cyber threat intelligence tools have become essential for organizations that want visibility, speed, and smarter defense decisions.
This guide explores leading platforms, real world use cases, and how to choose the right solution without overcomplicating your stack.
What Makes Cyber Threat Intelligence Tools Essential?

Modern security teams face phishing campaigns, ransomware operations, supply chain abuse, and zero day exploits. Raw data alone is not enough. Teams need context.
Cyber threat intelligence tools help by:
- Aggregating feeds from multiple sources
- Enriching indicators with context
- Prioritizing alerts
- Supporting faster investigation
Instead of reacting blindly, organizations gain structured insight.
Leading Cyber Threat Intelligence Platforms
1. Recorded Future

This platform delivers real time analysis using machine learning and open source collection. It provides risk scoring, brand monitoring, and vulnerability tracking. Many enterprises use it to improve detection precision.
2. Mandiant Advantage

Built by incident response experts, this solution focuses on adversary profiling and campaign tracking. It is widely adopted for strategic reporting and executive briefings.
3. IBM X Force Exchange
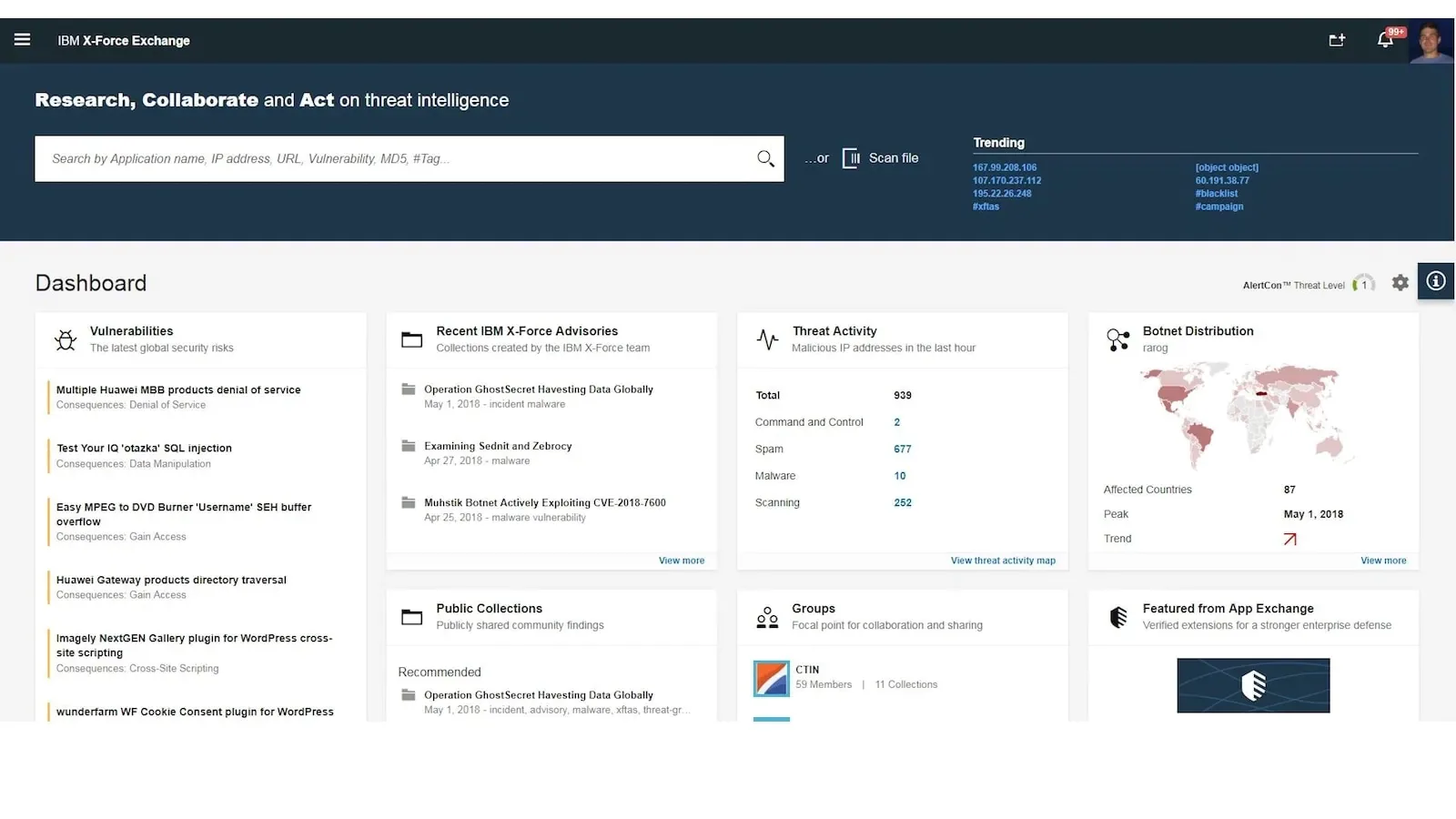
This cloud based system integrates with existing security ecosystems. It allows collaboration, data sharing, and investigation workflows across global teams.
4. ThreatConnect
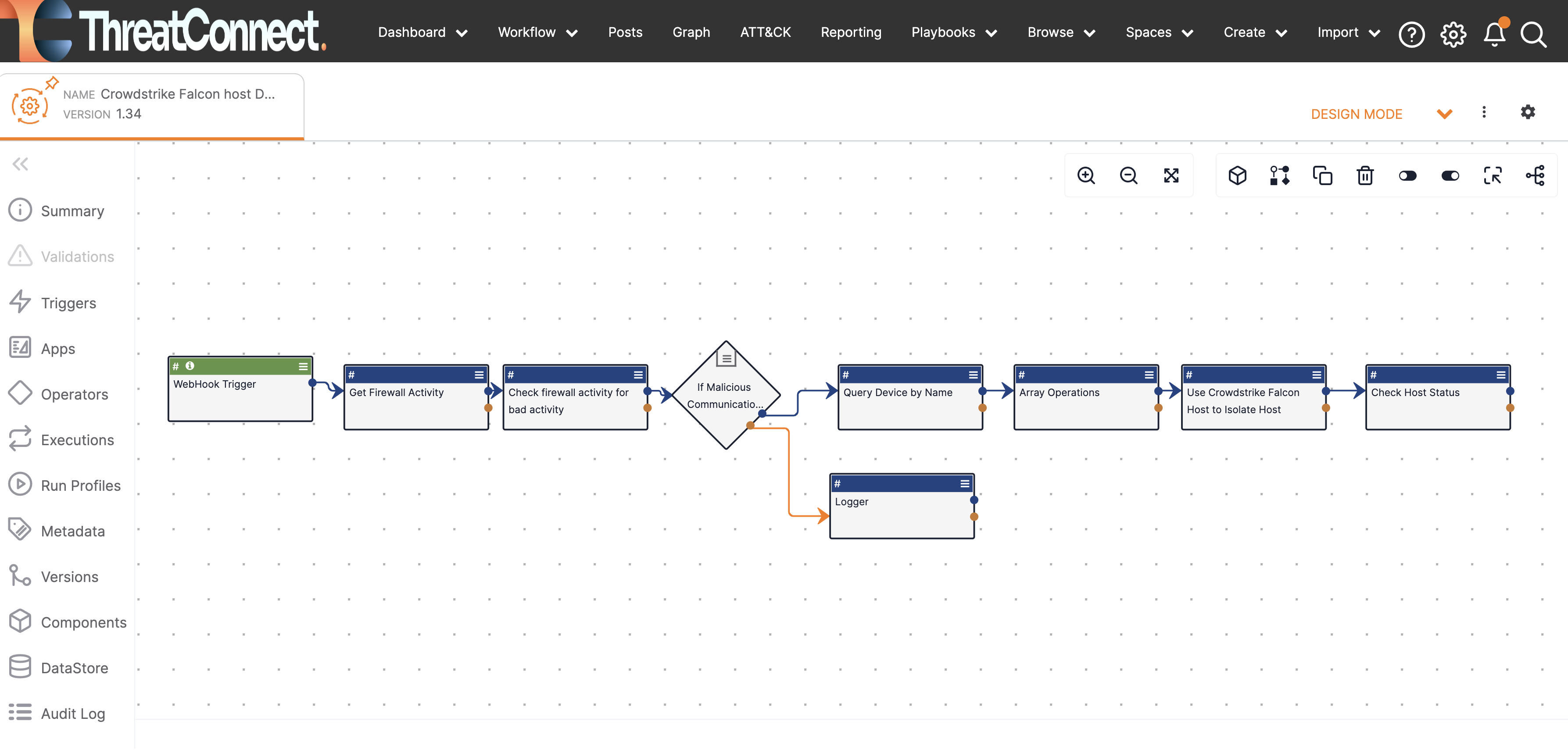
Known for automation and orchestration, this tool connects analysis with response. It supports playbooks, case management, and integration with SIEM systems.
5. Anomali ThreatStream
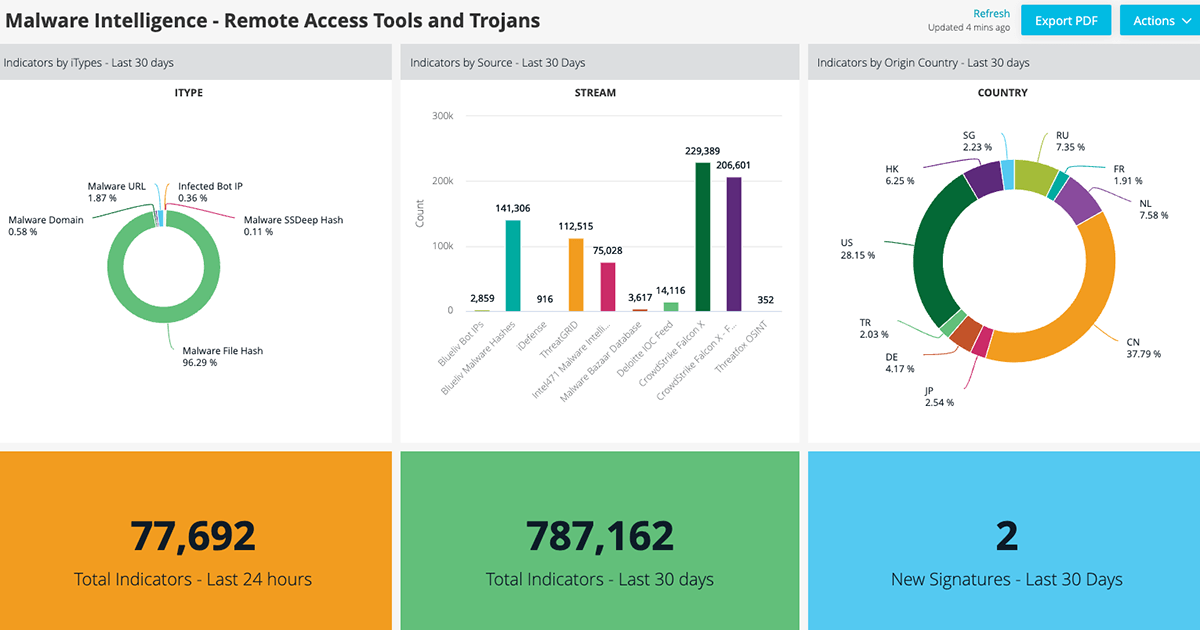
Designed for scalability, this option focuses on feed aggregation, enrichment, and prioritization. It fits both mid sized organizations and global enterprises.
Key Features to Look For
When evaluating cyber threat intelligence tools, focus on:
- Automated enrichment
- API integrations
- Real time alerts
- Reporting dashboards
- Collaboration features
- Customizable risk scoring
Avoid platforms that overwhelm teams with noise. Precision matters more than volume.
Strategic vs Operational Use
Cyber threat intelligence tools generally support three layers:
Strategic: Executive level risk trends
Operational: Campaign tracking and actor profiling
Tactical: Indicator based detection
Organizations benefit most when these layers connect seamlessly.
Implementation Best Practices

To maximize value:
- Define clear objectives
- Align with existing security controls
- Train analysts thoroughly
- Integrate with SIEM and SOAR tools
- Measure reduction in response time
Technology alone does not solve problems. Process alignment drives results.
Common Mistakes to Avoid
- Buying tools without workflow planning
- Ignoring data quality
- Failing to update feeds
- Overlooking integration requirements
- Treating intelligence as raw alerts
Smart teams treat intelligence as guidance, not noise.
The Future of Cyber Threat Intelligence Tools
Automation, AI assisted prioritization, and predictive analytics will shape the next generation of platforms. Integration across cloud, endpoint, and identity environments will become standard.
Organizations that invest early gain resilience, clarity, and stronger risk posture.
Final Thoughts
Cyber threat intelligence tools are no longer optional for serious security programs. The right platform improves visibility, reduces investigation time, and supports smarter decisions at every level.

